Introduction
Why Data Security Best Practices Matter
To avoid these consequences, call centers must implement robust data security best practices. By doing so, they can reduce risks and create a safer environment for both their customers and employees.
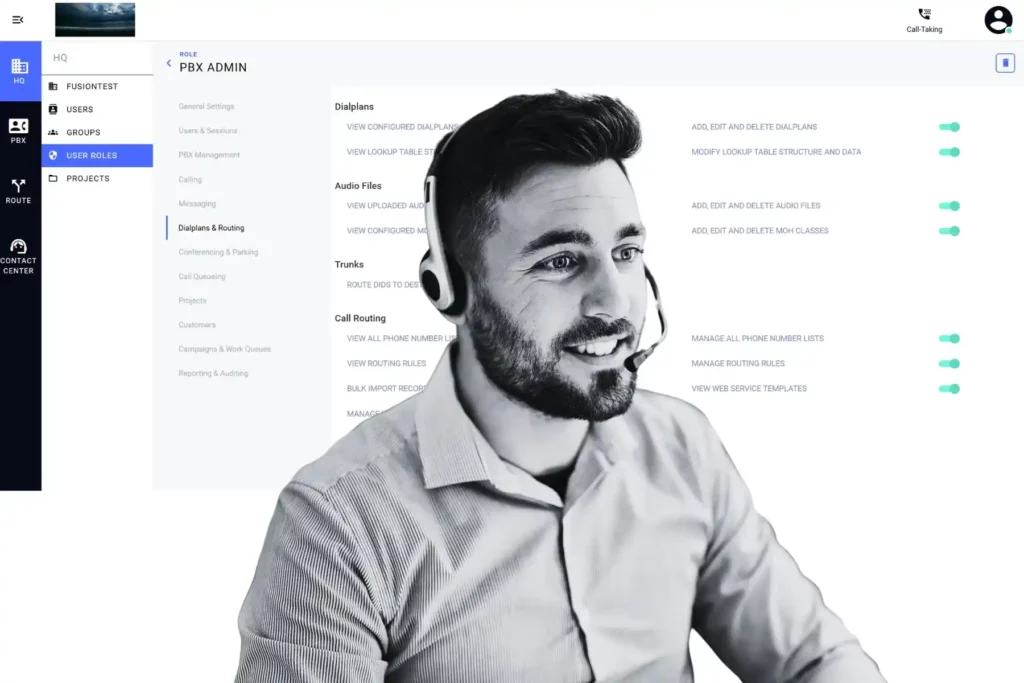
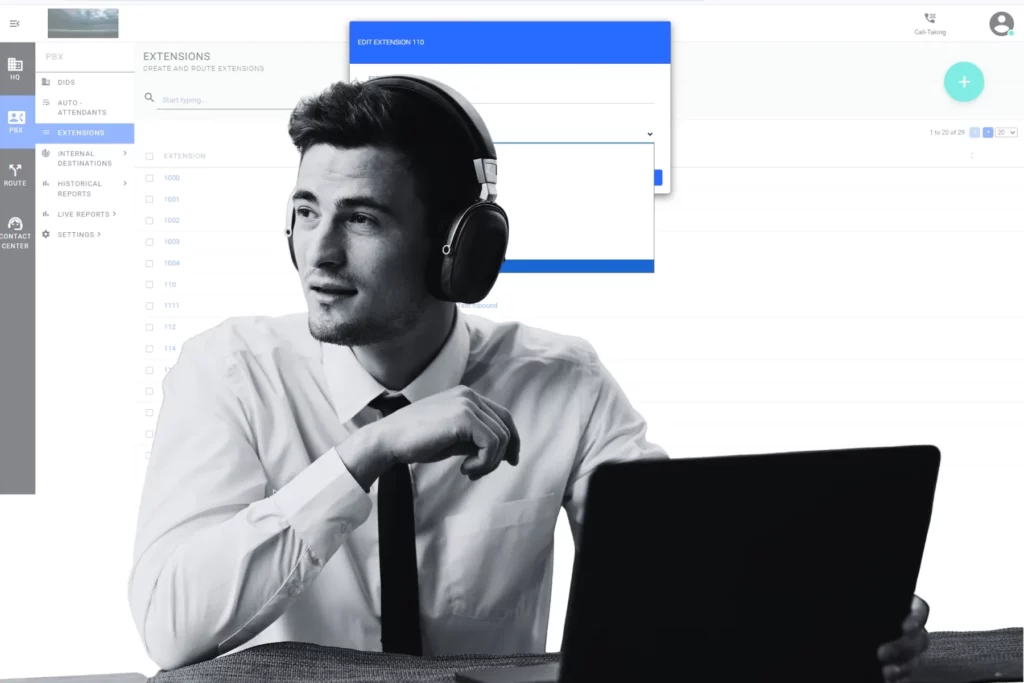
1. Role-Based Access Control: A Core Data Security Practice
- Why RBAC is essential: It minimizes the risk of insider threats and accidental data leaks by restricting unnecessary access.
- How to implement it effectively: Regularly review user permissions, revoke access when roles change, and add multi-factor authentication (MFA) for an extra layer of protection.
2. Data Encryption: Protecting Information at Every Stage
How to apply encryption effectively:
- Use SSL/TLS protocols to secure data in transit.
- Implement AES-256 encryption for data at rest.
- Regularly update and rotate encryption keys to avoid vulnerabilities..
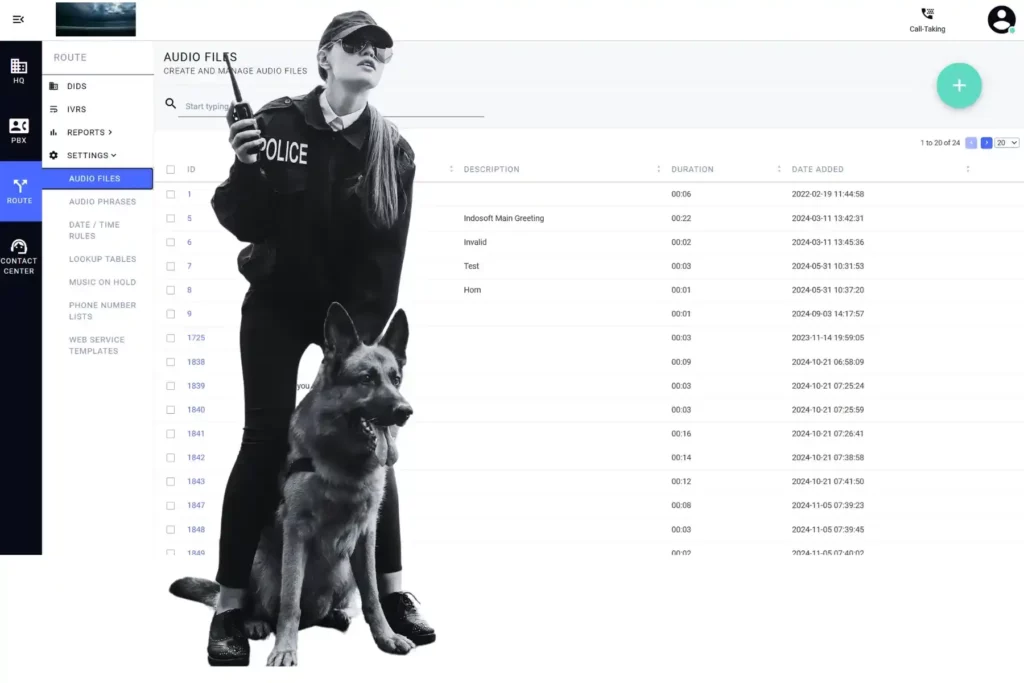
3. Employee Training: Strengthen Data Security Awareness
Training topics to prioritize:
- How to identify phishing emails and social engineering tactics..
- The importance of safeguarding login credentials.
- Procedures for reporting suspicious activity.
4. Strong Password Policies: A Simple Yet Crucial Practice
Best practices for secure passwords:
- Encourage passphrases with a minimum of 12 characters.
- Require a mix of uppercase letters, numbers, and symbols.
- Implement password expiration policies to prevent overuse.
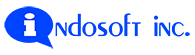
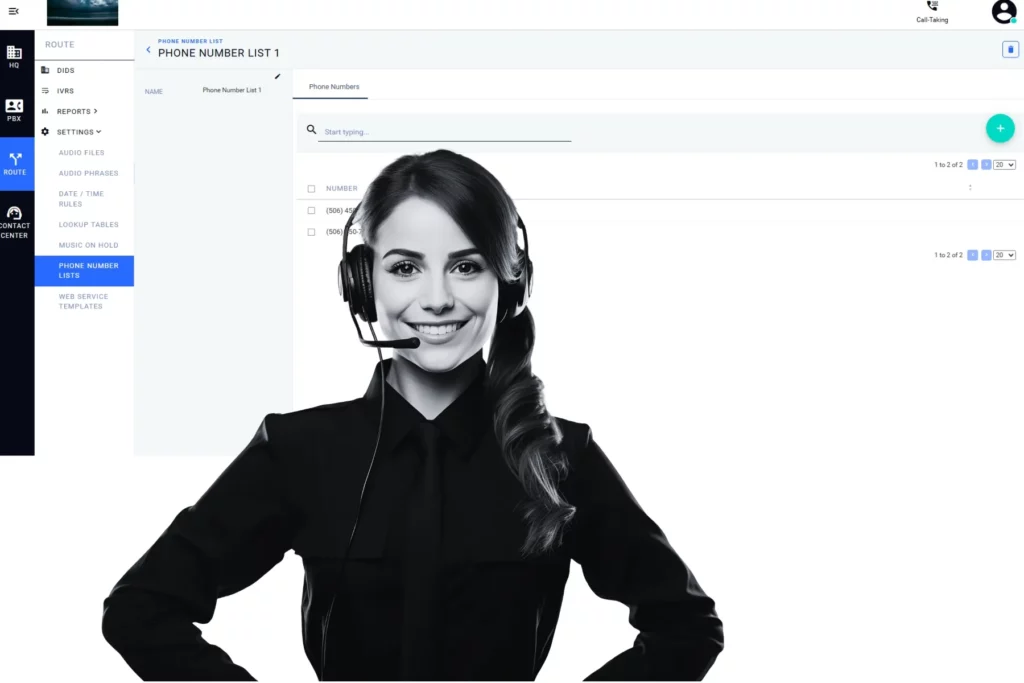
5. Continuous Monitoring: An Ongoing Data Security Practice
What to monitor:
- Login attempts from suspicious IP addresses.
- Anomalies in system performance that could signal malware.
- Unauthorized data access or unusual activity in logs.
6. Software Updates and Patching: Stay Ahead of Cybercriminals
How to maintain secure systems:
- Schedule automatic updates for critical tools.
- Conduct routine audits to identify and address unpatched vulnerabilities.
- Partner with a trusted IT team to stay informed about the latest threats.
7. Data Backups: Your Safety Net Against Attacks
Best practices for data backups:
- Follow the 3-2-1 rule: keep three copies of data, store it on two different media, and have one copy offsite.
- Encrypt backup data to prevent unauthorized access.
- Regularly test your backups to verify they can be restored.
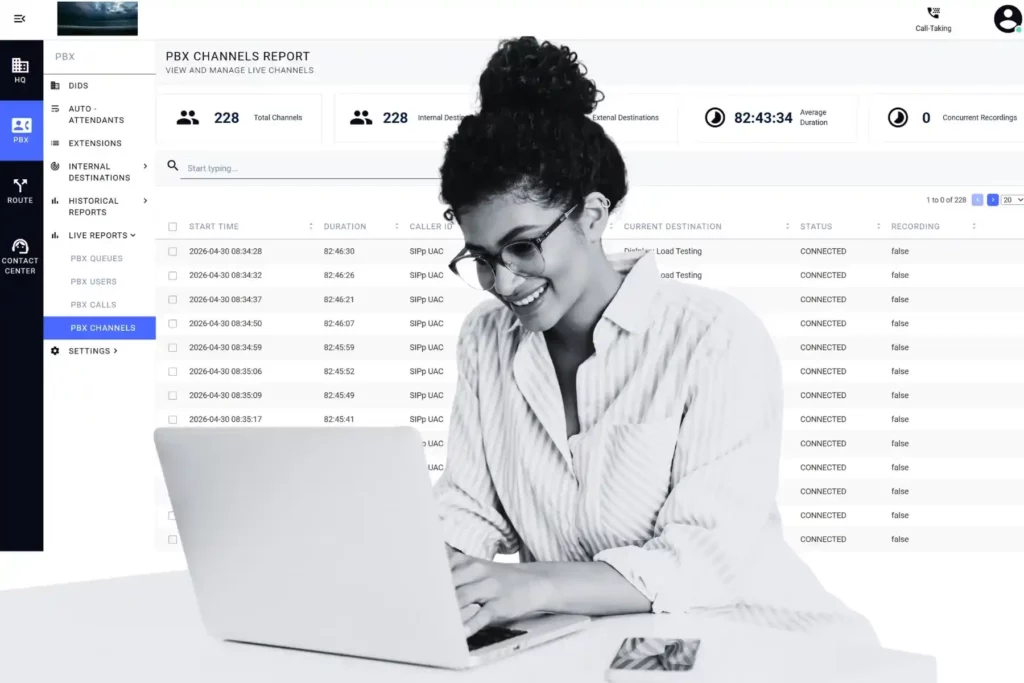
8. Compliance with Data Protection Regulations
Steps to achieve compliance:
- Understand the regulations that apply to your industry and region.
- Conduct regular audits to ensure all systems meet compliance requirements.
- Keep detailed records of security measures to demonstrate your commitment to protecting data.
Conclusion
articles
End-to-End Encryption in SIP
911 & Healthcare Call Recording for Contact Centers | QSuite NG
Contact Center Agent Turnover: Real Causes and Fixes
Call Center Software Evaluation: 6 Questions Managers Overlook
Call Center Agent Burnout: Smarter WFM Solutions
Phone System Troubleshooting Solutions for Call Centers
Cloud-Based PBX Deployment Strategy for Call Centers
Custom Contact Center Solutions: Build a Flexible Platform
Integrate Asterisk with CRM: Smarter Call Center Workflows
Omnichannel Customer Engagement Trends for 2026
Advanced Technology Agent Performance AI Asterisk Automation Call Center Call Center Management Call Center Software Call Routing Cloud Solutions Communication Cost Efficiency Customer Experience Customer Feedback Customers Customer Satisfaction Customer Service Customer Trust Cybersecurity Data Analysis and Reporting Data Security and Privacy Digital Customer Experience Efficiency Feedback Holiday Innovation Innovations in Customer Service Integration Loyalty Omnichannel Omnichannel Communication Omnichannel Support Operations Performance Personalized Customer Experience Productivity Real-Time Analytics and Reporting Service Solving Customer Problems Support Technology Top Trends Training Usability Workforce Management