Introduction
1. Enhance Software Security with Regular Assessments
Why it matters: The threat landscape is constantly changing. Therefore, older security measures may no longer protect against modern attack methods. Proactively testing your system ensures your defenses evolve alongside the latest threats.
Tip: Use a combination of automated tools and manual audits for comprehensive security checks. Regular assessments help you address new vulnerabilities as they emerge.
2. Leverage Multi-Factor Authentication for Stronger Security
Why it matters: Cybercriminals often exploit stolen credentials through phishing or brute-force attacks. MFA creates additional barriers that make it more difficult for attackers to gain access to sensitive systems.
Pro tip: Choose an MFA solution that balances security with user convenience to ensure widespread adoption.
3. Apply Security Patches Without Delay
Why it matters: Timely updates prevent attackers from exploiting software weaknesses. In fact, many breaches occur because organizations delay critical patches.
Pro tip: Automate updates wherever possible to avoid delays. If automation isn’t feasible, establish a robust update schedule and assign responsibilities to ensure timely execution.
4. Encrypt Data to Protect Sensitive Information
Why it matters: Even if attackers breach your system, encrypted data remains indecipherable without the appropriate decryption keys
Tip: Regularly review and update your encryption standards to ensure they meet industry best practices. Pair encryption with strong key management policies for optimal protection.
5. Enhance Security Awareness with Employee Training
Key focus areas:
- Recognizing phishing emails and malicious links
- Properly securing login credentials
- Reporting suspicious activity immediately
Why it matters: Even the most robust technical security measures can fail if employees are unaware of how to respond to threats.
Pro tip: Incorporate regular training sessions and interactive simulations to keep employees engaged and informed.
6. Adopt a Zero Trust Security Model
Why it matters: Traditional security models assume internal networks are secure, but with remote work and cloud computing becoming more prevalent, this assumption no longer holds true. A Zero Trust approach ensures that security is applied at every level.
Pro tip: Combine Zero Trust with endpoint protection tools for a comprehensive security framework.
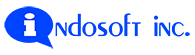
7. Monitor and Respond to Threats in Real-Time
Why it matters: Continuous monitoring reduces downtime and mitigates the impact of incidents by allowing for rapid response. Moreover, detecting threats early prevents small issues from escalating into larger ones.
Pro tip: Leverage AI-driven analytics to enhance threat detection capabilities and automate responses to common threats.
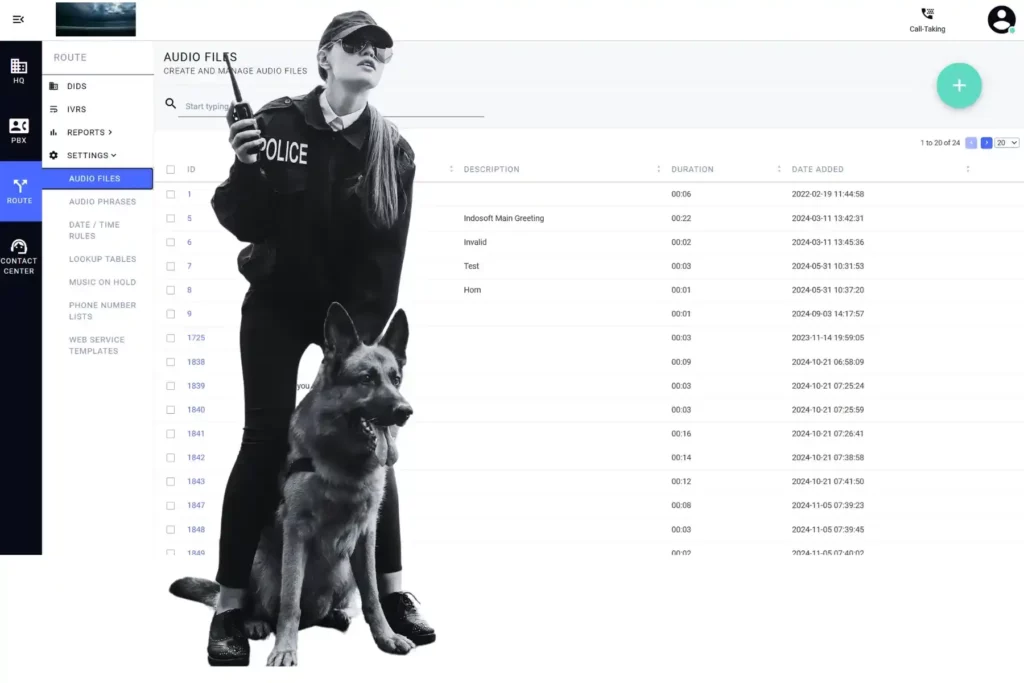
8. Secure Your APIs Against Exploits
Why it matters: Unsecured APIs can expose sensitive data and create entry points for attackers. Strengthening API security helps mitigate these risks.
Pro tip: Regularly test APIs for vulnerabilities, especially when introducing new integrations or updates. Additionally, monitor API usage to detect and prevent abuse.
9. Integrate DevSecOps to Embed Security in Development
Why it matters: Fixing security issues during development is faster, more cost-effective, and less disruptive than addressing them post-deployment.
Pro tip: Use automated tools to run security checks in your CI/CD pipeline. Regularly review and refine your processes to adapt to new challenges.
10. Back Up Your Data for Disaster Recovery
Why it matters: Even if attackers successfully compromise your systems, having a recent backup allows your organization to resume operations without paying ransoms or suffering prolonged downtime.
Pro tip: Follow the 3-2-1 backup rule: keep three copies of your data, store it on two different mediums, and maintain one copy offsite. Encrypt your backups for added security.
Final Thoughts: Take Action to Enhance Security
articles
End-to-End Encryption in SIP
911 & Healthcare Call Recording for Contact Centers | QSuite NG
Contact Center Agent Turnover: Real Causes and Fixes
Call Center Software Evaluation: 6 Questions Managers Overlook
Call Center Agent Burnout: Smarter WFM Solutions
Phone System Troubleshooting Solutions for Call Centers
Cloud-Based PBX Deployment Strategy for Call Centers
Custom Contact Center Solutions: Build a Flexible Platform
Integrate Asterisk with CRM: Smarter Call Center Workflows
Omnichannel Customer Engagement Trends for 2026
Advanced Technology Agent Performance AI Asterisk Automation Call Center Call Center Management Call Center Software Call Routing Cloud Solutions Communication Cost Efficiency Customer Experience Customer Feedback Customers Customer Satisfaction Customer Service Customer Trust Cybersecurity Data Analysis and Reporting Data Security and Privacy Digital Customer Experience Efficiency Feedback Holiday Innovation Innovations in Customer Service Integration Loyalty Omnichannel Omnichannel Communication Omnichannel Support Operations Performance Personalized Customer Experience Productivity Real-Time Analytics and Reporting Service Solving Customer Problems Support Technology Top Trends Training Usability Workforce Management
CONTACT US
Contact us for advanced software security solutions
At Indosoft, we specialize in providing cutting-edge security solutions tailored to your unique needs. Whether you’re looking for vulnerability assessments, real-time threat monitoring, or a comprehensive security strategy, our experts are here to help.